Documentation Index
Fetch the complete documentation index at: https://specterops-enable-tls-feedback.mintlify.app/llms.txt
Use this file to discover all available pages before exploring further.
Overview
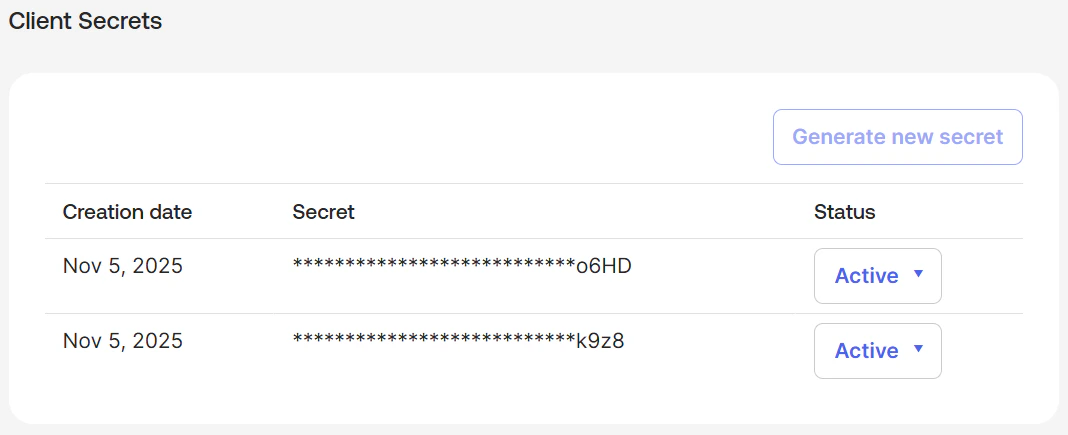
Client secrets are used by API service integrations and OIDC applications to authenticate with Okta and obtain access tokens.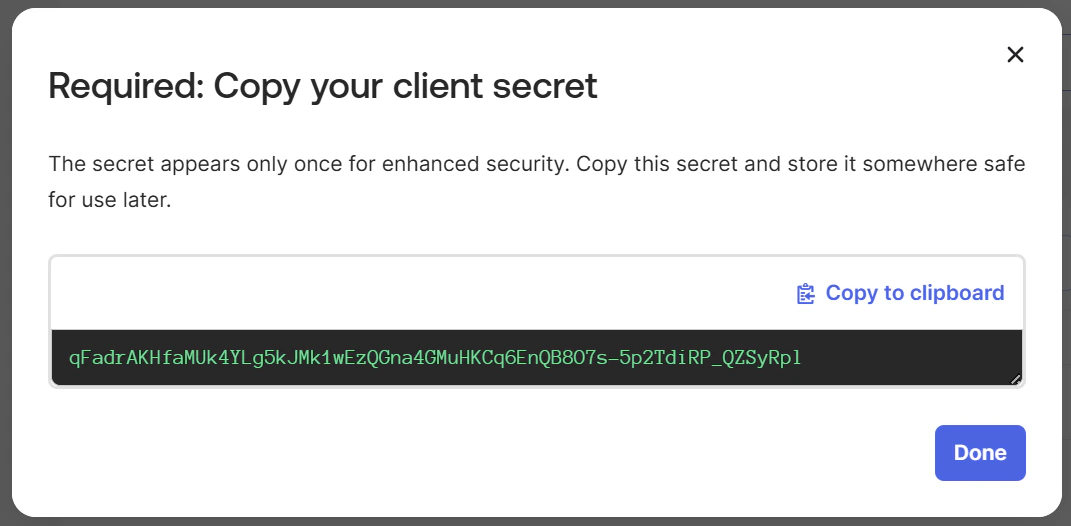
For security reasons, the OpenHound and OktaHound collectors do not collect client secrets, only their hashed identifiers.
Edges
The tables below list edges defined by the Okta extension only. Additional edges to or from this node may be created by other extensions.
Inbound Edges
| Edge Type | Source Node Types | Traversable |
|---|---|---|
| Okta_ReadClientSecret | Okta_User, Okta_Group, Okta_Application | ✅ |
Outbound Edges
| Edge Type | Destination Node Types | Traversable |
|---|---|---|
| Okta_SecretOf | Okta_Application, Okta_ApiServiceIntegration | ✅ |
Properties
| Name | Source | Type | Description |
|---|---|---|---|
id | secret.id | string | Unique client secret identifier. |
name | secret.secretHash | string | Hash of the secret value used as name/display label. |
displayName | secret.secretHash | string | Display label used in BloodHound. |
oktaDomain | Collector context (non-API) | string | Okta organization domain where the client secret exists. |
status | secret.status | string | Current lifecycle status of the secret. |
created | secret.created | datetime | Secret creation timestamp. |
lastUpdated | secret.lastUpdated | datetime | Last update timestamp for the secret metadata. |
Sample Property Values
For security reasons, the OktaHound collector does not write cleartext client secrets
to the OpenGraph JSON, only their hashed identifiers.


















